Server, Computer and network setup at a new Periodontal Clinic in Hoppers Crossing area. ———————————————Looking for a reliable and reputed IT company with years of experience in the dental industry to provide IT services or managed IT for your dental clinic? Then you have come to the right place. For more information visit:http://alphaclicl.com.au/services/it-for-dental-clinic/
Category: Case Studies
Business Telephone System Setup at New Castle in September 2018
Does AlphaClick provide IT services in Newcastle?YES, we provide IT services in all around Victoria, New South Wales and Queensland. Does AlphaClick provide business telephone systems?YES, we are experts not just in managed IT services. We provide phone systems, web design, SEO and much more.. all your IT needs under one umbrella. ——————————————— Here are […]
Data backup – Why is it important for your business?
Some of you may be aware and some may not that data/information is one of the most valuable assets in your business. In today’s world, most of the businesses heavily depend on computers and technology and almost all of their information such as financial information, HR information, and a lot of other information is stored […]
Top 10 Ransomware Attacks in Australia and Other Countries of the World
Ransomware is a type of malware which locks the computer data with encryption and holds it for ransom until the payment is made. The data is decrypted and access is granted to the user only when the payment is done. Money is the main motive for these malicious attacks that often spread through infected software […]
Average Internet Speed in Australia
Australia falls to 55th place in average internet speed in comparison to other countries. Top 5 Countries with fast inernet:1. Singapore – 161.21 Mbps2. Iceland – 145.64 Mbps 3. Hong Kong – 141.56 Mbps4. South Korea – 132.52 Mbps5. Romania – 98.64 Mbps And this is where Australia stands:55. Australia – 25.88 Mbps56. United Arab Emirates […]
Business Information Security
Information Security Are you aware of the latest Privacy Act 2017? Latest Privacy Act 2017 – Notifiable Data Breaches (NDB) – Effective from 22nd February 2018 What is NDB? In a nutshell, Potential impact on your business What do you need to do? How can AlphaClick help you? About Us We are a friendly IT […]
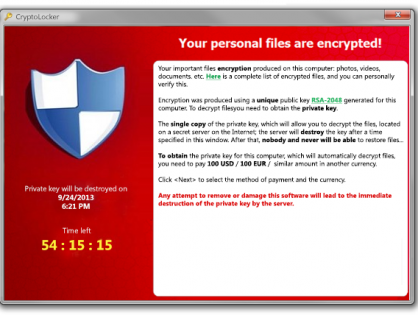
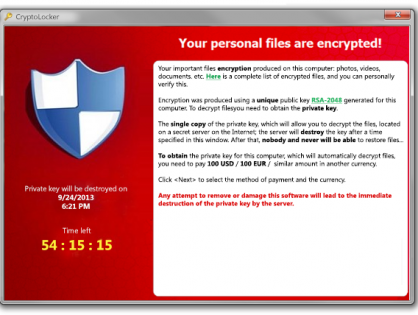
Cryptolocker Virus and Ransomware
Cryptolocker Virus and Ransomware Ransomware is a type of malware that prevents or limits users from accessing their system, either by locking the system’s screen or by locking the users’ files unless a ransom is paid. More modern ransomware families, collectively categorized as crypto-ransomware, encrypt certain file types on infected systems and forces users to […]
Email Virus
Email Virus What is are email viruses? How can you be protected? How can we help you? Example: The attached image is one of the examples.
Migrating to Cloud Email System
Most organizations, especially small/medium organizations may not fully understand the differences between POP vs IMAP vs Cloud email systems. And amongst these organizations, most of them still use POP/IMAP email systems. There are many advantages of migrating your business email system to a cloud system such as Google Apps (G Suite) or Microsoft Office 365. […]
What is Ransomware?
What is ransomware? This is a type of malicious software developed by computer hackers to block your data by encrypting until a ransom is paid. How does ransomware get into your system? Ransomware is mainly distributed via email attachments. The hackers make the emails and attachments look legitimate to make sure the users easily fall […]